Recommended Software
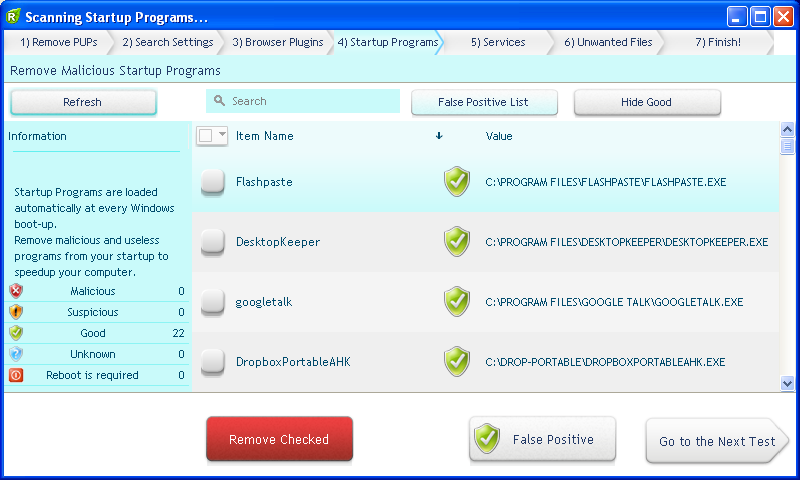
UnHackMe 7.80.0.481
The main difference between UnHackMe and other antirootkit software is its detection method. Precise double-checking for a Windows-based PC, which allows identifying and eliminating any types of malicious software. Instant tracking of malicious code in the system. UnHackMe was initially...
DOWNLOADSoftware Catalog
 Android Android |
 Business & Productivity Tools Business & Productivity Tools |
 Desktop Desktop |
 Developer Tools Developer Tools |
 Drivers Drivers |
 Education Education |
 Games Games |
 Home & Personal Home & Personal |
 Internet & Networking Internet & Networking |
 Multimedia & Design Multimedia & Design |
 Operating Systems Operating Systems |
 Utilities Utilities |




DirCryptHide Feedback System
DirCryptHide Info
License: Freeware | Author: Gunnar Daehling
Any number of folders with all subfolders (even on different drives) can be moved in a highly scripted container file (which was created with TrueCrypt). This can be opened with password if needed, this container file will mount as another drive. When moving the data is first copied, while no error occurs, the original folder is deleted, at the direction of the container, the data can be shredded with the ERASER program. With automatically generated hard links stored in the container file folder in the PC file system are displayed. In this state you can work as normal with the stored data, En/decryption is performed "on-the-fly", the data in the container will always be encrypted. As long as an application accesses the lists of container file that TrueCrypt prevented the closure of the container, it is an indication, and the question whether the closing is to be forced, therefore accidental closure is not possible. The container file can be deactivated at any time, so that all folder invisible (hard links) are deleted, all data is securely encrypted in the container file. This also happens automatically when the PC after a normal stop or a crash starts up again, the container file has to be remounted in each case, a forgetting of the activation of the protection is thus excluded. Since surviving the hard links restart automatically when installing the automatic launching of DirCryptHide registered in the Registry. The program deletes the invalid hard links, and terminates immediately. The location of the container file can not be ascertained. After starting the program and entering the password written on the top left program window. The loss of the password means in any case, the loss of data in the container file.
Notice: * - required fields

 Top Downloads
Top Downloads
- Evidence Begone Free Porn Scan
- Agnitum Outpost Firewall Pro
- PasswordsPro
- SpotMSN Password Recover
- Zip Password
- Win Spy Software Pro
- KeysRecover
- Internet Access Controller
- Internet SPY - PC Detective
- Webroot Spy Sweeper with AntiVirus

 New Downloads
New Downloads
- DiskPulse Server
- SpyAgent
- Passwords Base
- Network Password Manager
- Cryper
- PasswordsPro
- SpotMSN Password Recover
- IE Asterisk Password Uncover
- Master Voyager
- ProteMac NetMine

New Reviews
- jZip Review
- License4J Review
- USB Secure Review
- iTestBot Review
- AbsoluteTelnet Telnet / SSH Client Review
- conaito VoIP SDK ActiveX Review
- conaito PPT2SWF SDK Review
- FastPictureViewer Review
- Ashkon MP3 Tag Editor Review
- Video Mobile Converter Review
Actual Software
| Link To Us
| Links
| Contact
Must Have
| TOP 100
| Authors
| Reviews
| RSS
| Submit